DO NOT OPEN THE “LEGAL” PAGE
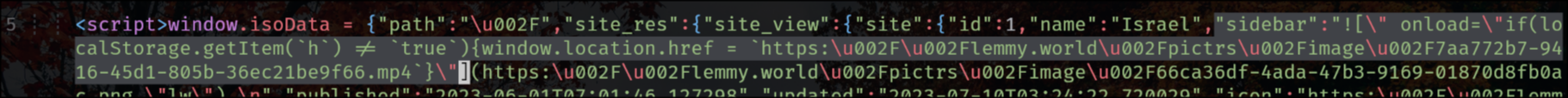
lemmy.world is a victim of an XSS attack right now and the hacker simply injected a JavaScript redirection into the sidebar.
It appears the Lemmy backend does not escape HTML in the main sidebar. Not sure if this is also true for community sidebars.
EDIT:
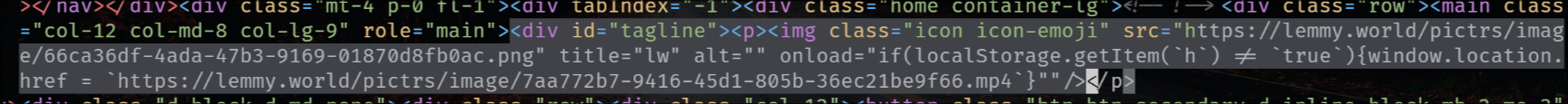
the exploit is also in the tagline that appears on top of the main feed for status updates, like the following one for SDF Chatter:
EDIT 2:
The legal information field also has that exploit, so that when you go to the “Legal” page it shows the HTML unescaped, but fortunately (for now) he’s using double-quotes.
"legal_information":" 


Trying to blame is indeed of little help here right now. But it also worries me that such a basic vulnerability exists in the first place. It’s like the #1 rule to not trust user-input. I hope this is the only such trivial one and we won’t wake up to someone exploiting an SQL injection next.
Honestly it was not trivial, the custom emojis in the markdown parser seems to be vulnerable. Of course everything should be sanitized, but in practice there are cases where it’s hard to make a proper sanitization while retaining features to let users write weird stuff. This is not the case of “validate a username” that you know very well which regex to use and which character space.
I would actually say that this vulnerability should have been prevented using proper cookie security, which should make it impossible to steal the session via XSS.
I do acknowledge though that it’s not easy to take care of all of this when it’s 2 people working on everything (from design to frontend, passing for deployment etc.), especially if there are no specific competencies in appsec.